Content
Why is this necessary?
So, you have decided to take the delivery of emails under personal control and want to set up digital signatures for your domains? We already have articles where we simply and in details paint the setting of each of them.
In the same article, we decided to give a general look at the technology and describe the sequence of settings, without going into details. Also we will note everything that is needed in the process, except for the signatures themselves.
The essence of the technology is simple: you as the owner of the domain from which the mailings are conducted can register in the DNS of your domain a policy that determines what to do with emails that are recognized as counterfeit. Implementation may seem intricate, but the picture from Gmail.com perfectly visualizes the essence.
What sequence?
Your domain
Of course, you will need your domain. We only note that we recommend using the services of trusted registrars. For example, GoDaddy.
By the way, you can bind the purchased domain to us or not. You can find variants and binding possibilities here.
Corporate Mail
Undoubtedly you will need your own corporate mail and not only one. Often this service is provided by your hoster, but you can also use the free services from the mailing giants. More detailed instructions are in this article.
Dedicated IP
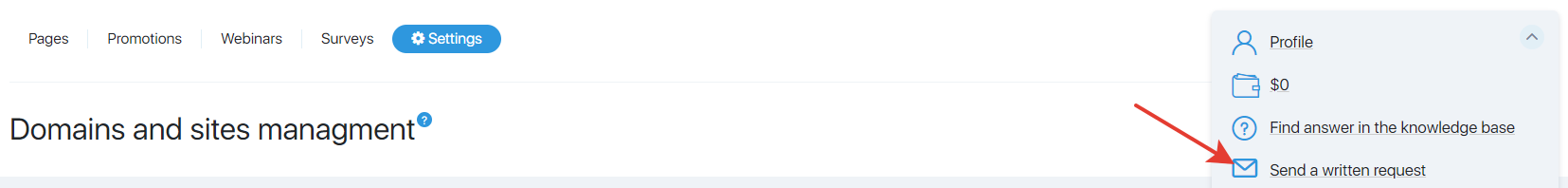
If everything described above is already there, then boldly write to support. The most convenient way to do this is from a personal cabinet.
First you need to send a request to connect a dedicated server to an IP with a good reputation. Example query:
Theme: “Providing a dedicated IP for mailings”
Message: “My tariff is Guru. My login: login Configure, please, the dedicated IP for mailings.”
DKIM signature
DKIM is one way to make sure that the letter is not forged and has been sent by the actual owner of the mailing address. Its configuration is the first step in setting up digital signatures of the email. This step, by the way, is not mandatory, but necessary for you to be able to get information about what happens to your emails first-hand – that is, from the mailing services your subscribers and customers use. You can configure the DKIM signature simultaneously with the configuration of the dedicated IP. That is, you can send 2 requests at once. Detailed instructions for configuring the DKIM signature can be found in this article.
SPF and DMARC
Thanks to the SPF (Sender Policy Framework), you can check whether the sender’s domain has been tampered with.
DMARC is a specification designed to reduce the number of spam and phishing emails based on the identification of the sender’s email domains by other characteristics that do not take into account DKIM or do not fully take into account the SPF.
Altogether, these settings give the best results. A detailed description and instructions for setting up these records can be found here.
Connecting Monitoring Tools
Connect the “Post Office” from PostMaster from Gmail.com in order to track the delivery, opening-rate and spamming-rate of your emails using Gmail services.
FBL for your domains
FBL is the standard for issuing information about complaints, about spam from an email service provider to the sender of emails. Mail.ru, Yandex and Google are the only mail services that use this technology. For more information about this setting, see this article.
Who is a fine fellow?
You are! Well done! Did you really manage to set it all up? We must admit that the list was quite frightening. Of course, in reality it was something much easier than it looked at first glance. You made some adjustments, and now everything is ready and working, you feel great! ?